
TECHNICAL VALIDATION
How to Deliver Successful AI Projects by Reducing Risk and Boosting Performance
Google Cloud Security Ecosystem—Palo Alto Networks
How to Deliver Successful AI Projects by Reducing Risk and Boosting Performance
Leveraging the Google Platform to Accelerate the
Delivery of Differentiated Security Offerings
By Tony Palmer, Practice Director and Principal Analyst, Validation Services
Enterprise Strategy Group
December 2023
Introduction
Background
Figure 1. Cloud-first Policy for New Applications on the Rise

The Google Cloud Security Ecosystem
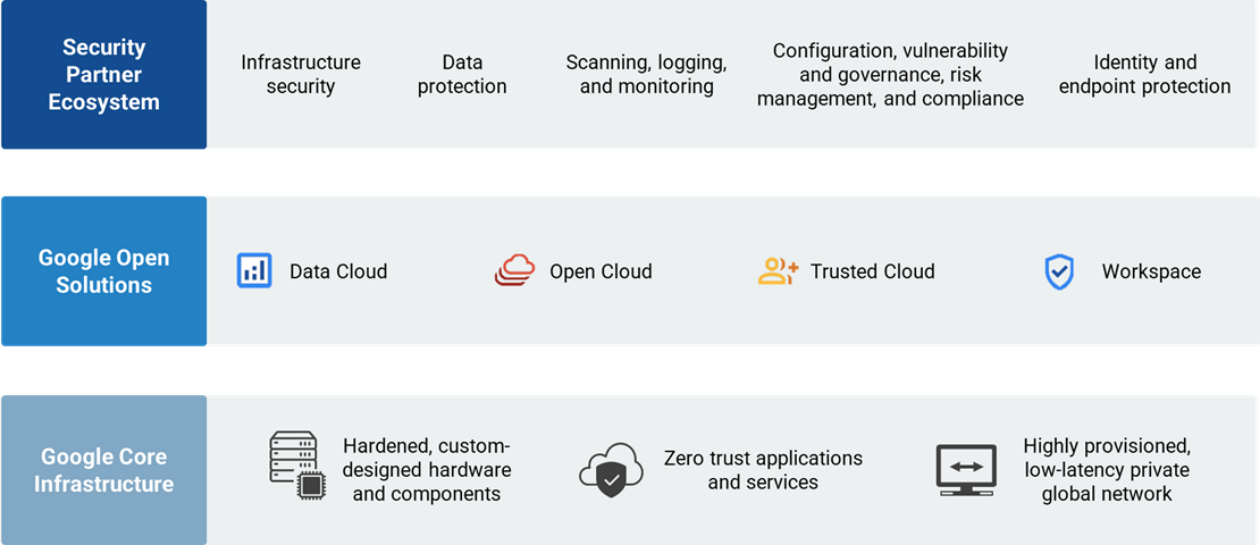
Google Cloud is designed, built, and operated with security as a primary design principle to help protect its customers against threats in their environments. Google layers on security controls to enable organizations to meet their own policy, regulatory, and business objectives. Customers can leverage elements of Google’s compliance framework in their own compliance programs.
Google Cloud secures more than three billion users globally. To accomplish that, Google’s cloud infrastructure can’t rely on any single technology to make it secure. Google’s stack builds security through progressive layers designed to deliver true defense in depth, and at scale.
Figure 2. Google Cloud Security Ecosystem Overview
Source: Enterprise Strategy Group, a division of TechTarget, Inc.
Google Workspace

Enterprise Strategy Group Technical Validation
Palo Alto Networks—OEM
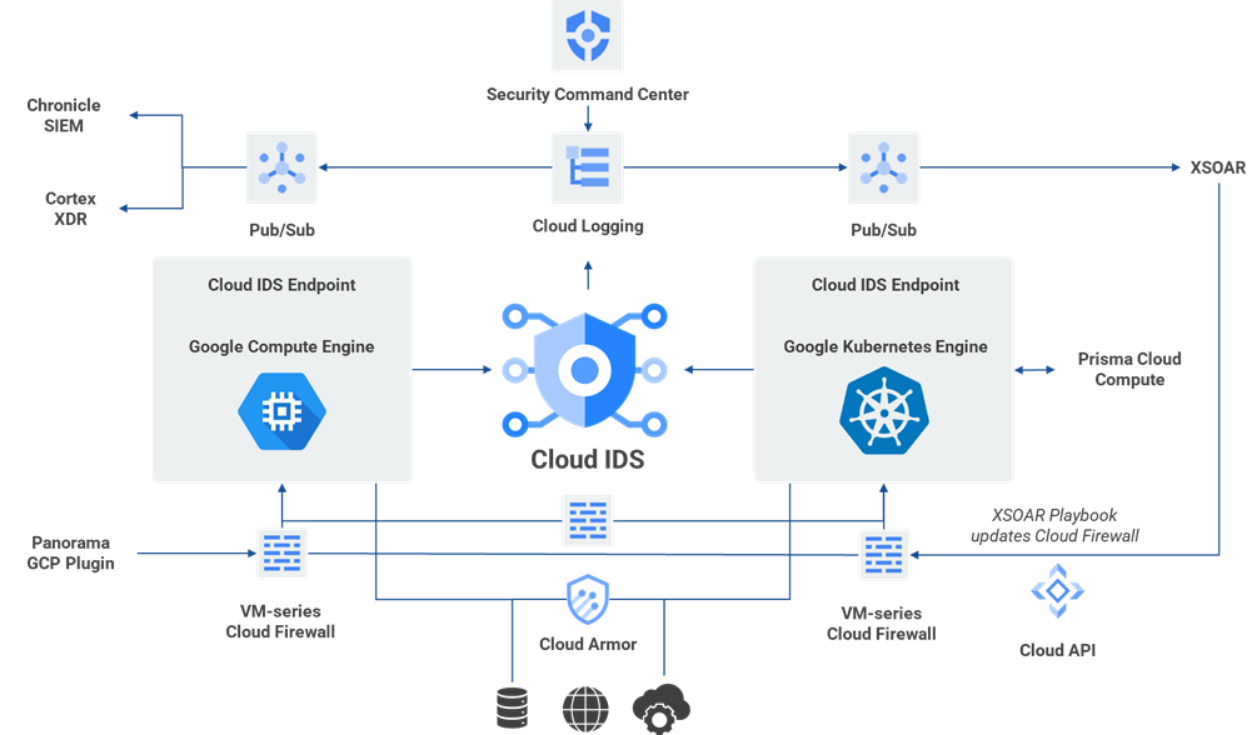
Figure 3. Cloud IDS Reference Architecture for Palo Alto Networks on Google Cloud
Source: Google and Enterprise Strategy Group, a division of TechTarget, Inc.

Why This Matters
Enterprise Strategy Group research shows that organizations have faced a wide range of attacks on their cloud-native applications, making it clear that they need to take steps to reduce their security risk. Eighty- eight percent of organizations reported having been attacked across a wide range of incidents, including malware moving laterally across workloads, targeted penetration attacks, and exposed or lost data from an object store.
Google Cloud partnered with Palo Alto Networks to develop and deliver Cloud IDS to provide cloud-native threat detection that detects network-based threats, such as malware, spyware, and command-and-control attacks with both north-south and east-west traffic visibility. Customers benefit from a cloud-native, managed experience that combines high performance and high-fidelity network-based threat data for investigation and correlation with the simple, secure, and scalable infrastructure of Google Cloud.
Detecting threats in traffic between workloads within the trust boundary of a VPC has been a significant challenge for cloud network security teams. With Cloud IDS, Google Cloud customers can deploy on-demand application visibility and threat detection between workloads or containers in any Google Cloud VPC to support their compliance goals and protect applications.
Palo Alto Networks leveraged the foundational capabilities of Google Cloud’s infrastructure and Google Cloud’s first-party tools to create and deliver differentiated products and offerings to their customers. In turn, Google is leveraging Palo Alto Networks’ expertise in an OEM relationship to deliver differentiation and enhance the value of Google Trusted Cloud.
Conclusion
This Enterprise Strategy Group Technical Validation was commissioned by Google and is distributed under license from TechTarget, Inc.
©TechTarget, Inc. or its subsidiaries. All rights reserved. TechTarget, and the TechTarget logo, are trademarks or registered trademarks of TechTarget, Inc. and are registered in jurisdictions worldwide. Other product and service names and logos, including for BrightTALK, Xtelligent, and the Enterprise Strategy Group might be trademarks of TechTarget or its subsidiaries. All other trademarks, logos and brand names are the property of their respective owners.
Information contained in this publication has been obtained by sources TechTarget considers to be reliable but is not warranted by TechTarget. This publication may contain opinions of TechTarget, which are subject to change. This publication may include forecasts, projections, and other predictive statements that represent TechTarget’s assumptions and expectations in light of currently available information. These forecasts are based on industry trends and involve variables and uncertainties. Consequently, TechTarget makes no warranty as to the accuracy of specific forecasts, projections or predictive statements contained herein.
Any reproduction or redistribution of this publication, in whole or in part, whether in hard-copy format, electronically, or otherwise to persons not authorized to receive it, without the express consent of TechTarget, is in violation of U.S. copyright law and will be subject to an action for civil damages and, if applicable, criminal prosecution. Should you have any questions, please contact Client Relations at cr@esg-global.com.
About Enterprise Strategy Group
TechTarget’s Enterprise Strategy Group provides focused and actionable market intelligence, demand-side research, analyst advisory services, GTM strategy guidance, solution validations, and custom content supporting enterprise technology buying and selling.
