
Brought to you by:
Enterprise Strategy Group | Getting to the Bigger Truth™
TECHNICAL VALIDATION
Secure Applications at Runtime with the Waratek ARMR Security-as-Code Platform
Runtime Code Patching to Prevent Exploits at the Source
By Justin Boyer, IT Validation Analyst; and Tony Palmer, Principal IT Validation Analyst
JULY 2022
Introduction
Background
Figure 1. Companies Often Push Known Vulnerable Code to Production, Increasing Risk Exposure
Has your organization ever pushed code to production with known organic vulnerabilities? (Percent of respondents, N=378)
Source: ESG, a division of TechTarget, Inc.

The Waratek ARMR Security-as-Code Platform
Figure 2. Waratek Protects Applications at Runtime by Swapping in Secure Code
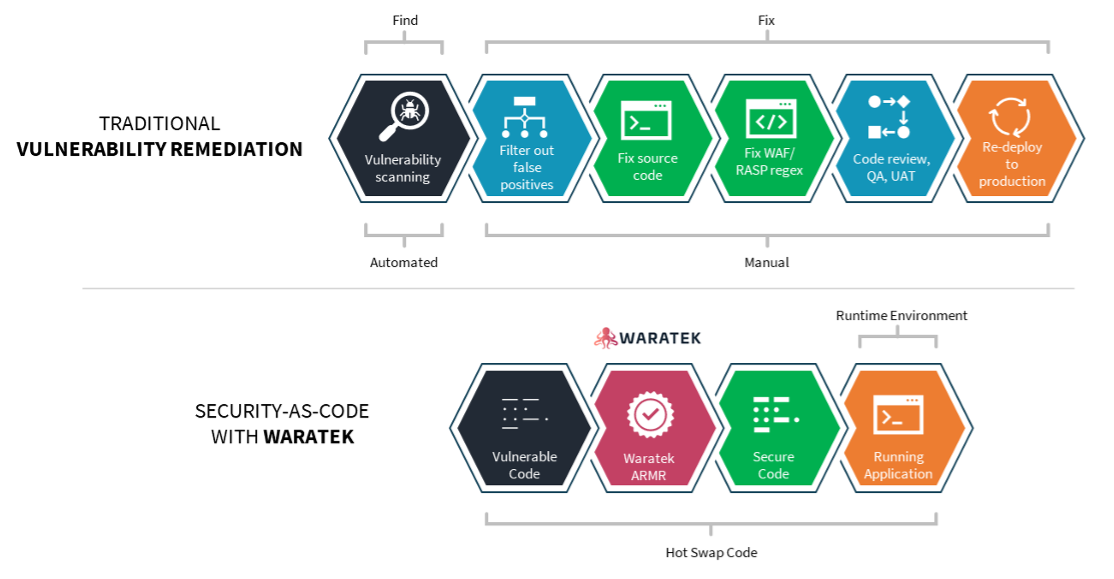
Source: ESG, a division of TechTarget, Inc.
ESG Technical Validation
Declarative Security-as-Code
Figure 3. Successful SQL Injection Attack
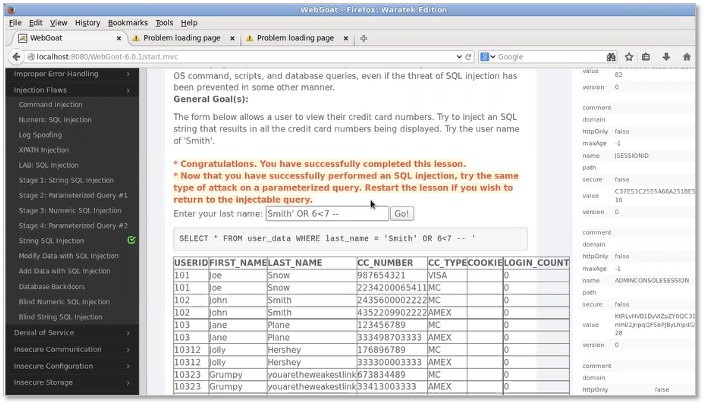
Source: ESG, a division of TechTarget, Inc.
Figure 4. Waratek ARMR Rule Creation
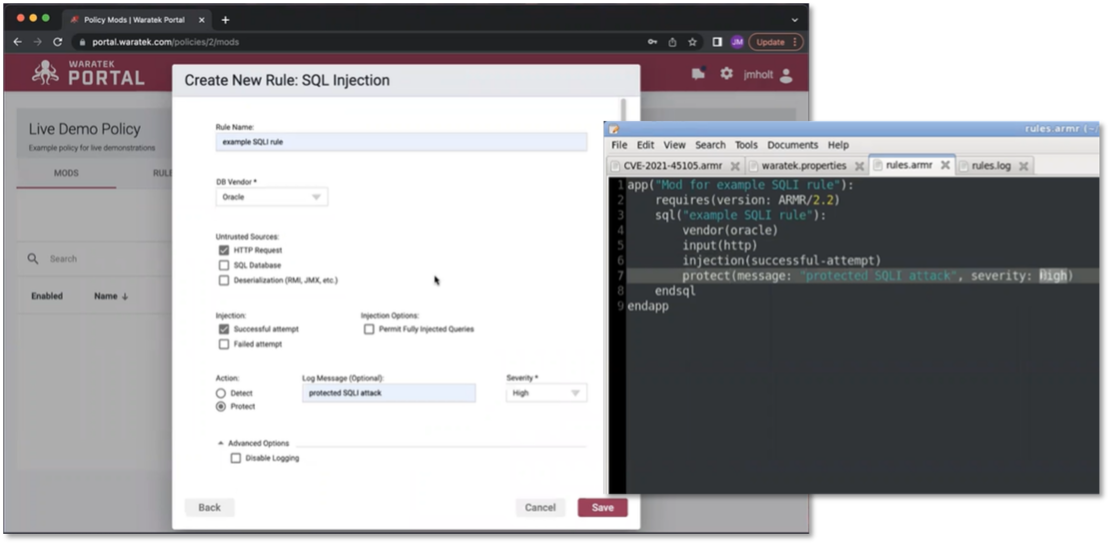
Source: ESG, a division of TechTarget, Inc.
Figure 5. Waratek Stops the SQL Injection Attack Without Changing the Application Code
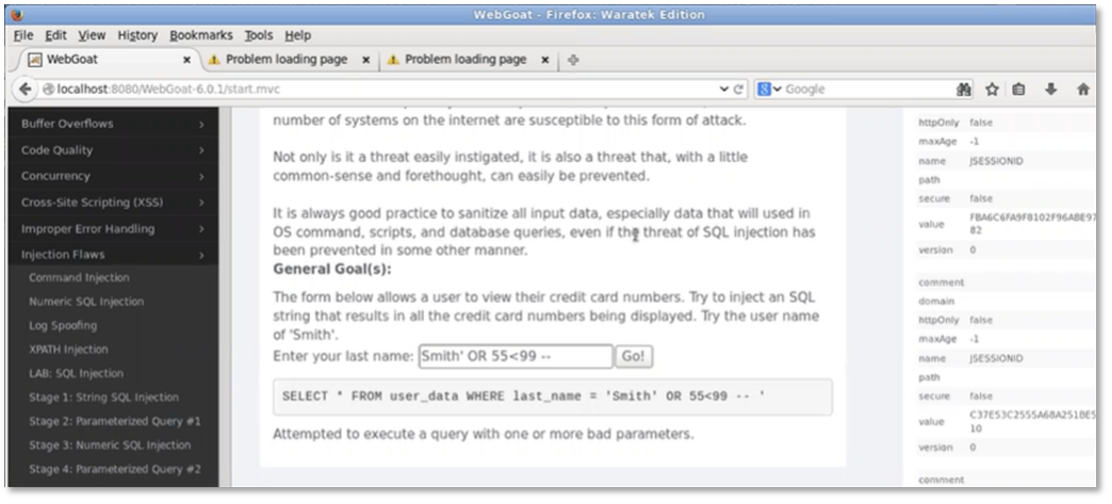
Source: ESG, a division of TechTarget, Inc.
The Power if JIT Compilation — For Security-as-Code
Figure 6. Waratek Logs Protection Events
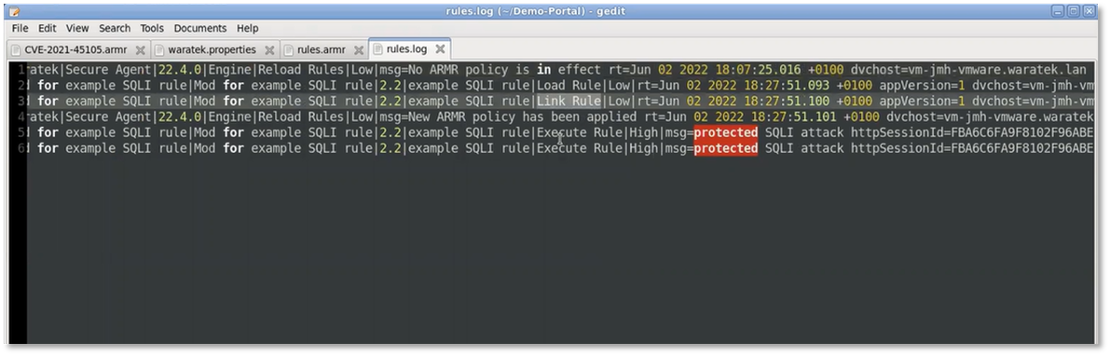
Source: ESG, a division of TechTarget, Inc.
Why This Matters
The Bigger Truth
This ESG Technical Validation was commissioned by Waratek and is distributed under license from TechTarget, Inc.
All product names, logos, brands, and trademarks are the property of their respective owners. Information contained in this publication has been obtained by sources TechTarget, Inc. considers to be reliable but is not warranted by TechTarget, Inc. This publication may contain opinions of TechTarget, Inc., which are subject to change. This publication may include forecasts, projections, and other predictive statements that represent TechTarget, Inc.’s assumptions and expectations in light of currently available information. These forecasts are based on industry trends and involve variables and uncertainties. Consequently, TechTarget, Inc. makes no warranty as to the accuracy of specific forecasts, projections or predictive statements contained herein.
This publication is copyrighted by TechTarget, Inc. Any reproduction or redistribution of this publication, in whole or in part, whether in hard-copy format, electronically, or otherwise to persons not authorized to receive it, without the express consent of TechTarget, Inc., is in violation of U.S. copyright law and will be subject to an action for civil damages and, if applicable, criminal prosecution. Should you have any questions, please contact Client Relations at cr@esg-global.com.
The goal of ESG Validation reports is to educate IT professionals about information technology solutions for companies of all types and sizes. ESG Validation reports are not meant to replace the evaluation process that should be conducted before making purchasing decisions, but rather to provide insight into these emerging technologies. Our objectives are to explore some of the more valuable features and functions of IT solutions, show how they can be used to solve real customer problems, and identify any areas needing improvement. The ESG Validation Team’s expert third-party perspective is based on our own hands-on testing as well as on interviews with customers who use these products in production environments.

Enterprise Strategy Group | Getting to the Bigger Truth™
Enterprise Strategy Group is an IT analyst, research, validation, and strategy firm that provides market intelligence and actionable insight to the global IT community.